The content below is taken from the original ( Admin Essentials: Improving Chrome Browser extension management through permissions), to continue reading please visit the site. Remember to respect the Author & Copyright.
IT teams often look for best practices on managing extensions to avoid exposing company IP, leaving open security holes and compromising the productivity of end users. Fortunately, there are several options available to admins for extension management in Chrome. I’m going to cover one of them in more detail in this Admin Essentials post.
Several configuration options are available to enterprises wanting to manage extensions. Many enterprises are familiar with the more traditional route of blacklisting and whitelisting. But a second approach offers enterprises more granular controls. Instead of managing the extensions themselves, you can block or allow them by their behavior or permissions.
What are extension permissions?
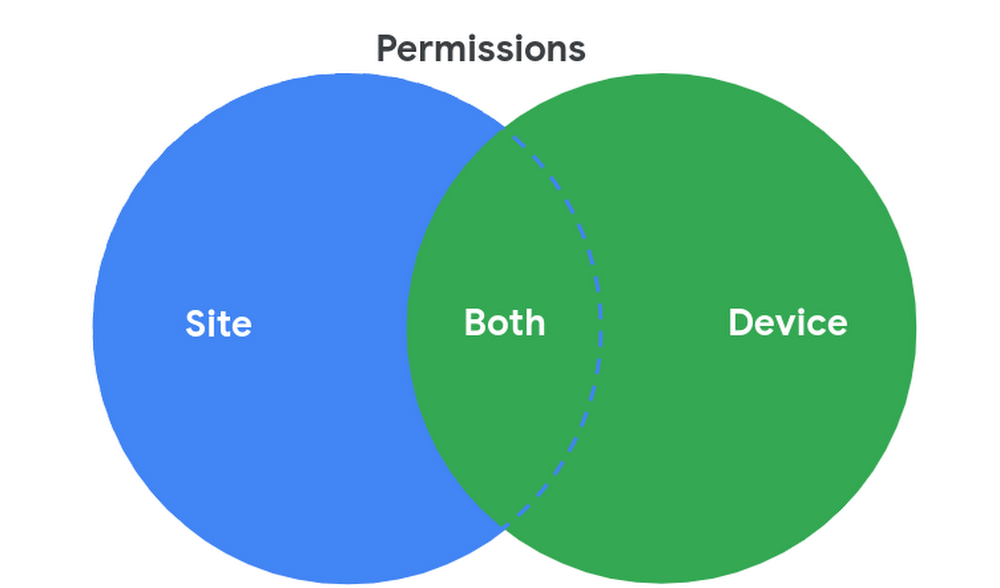
Permissions are the rights that are needed on a machine or website in order for the extension to function as intended. There are device permissions that need access to devices and site permissions that need access to sites. Some extensions require both.
Permissions are declared by the extension developer in the manifest file. Here is an example:
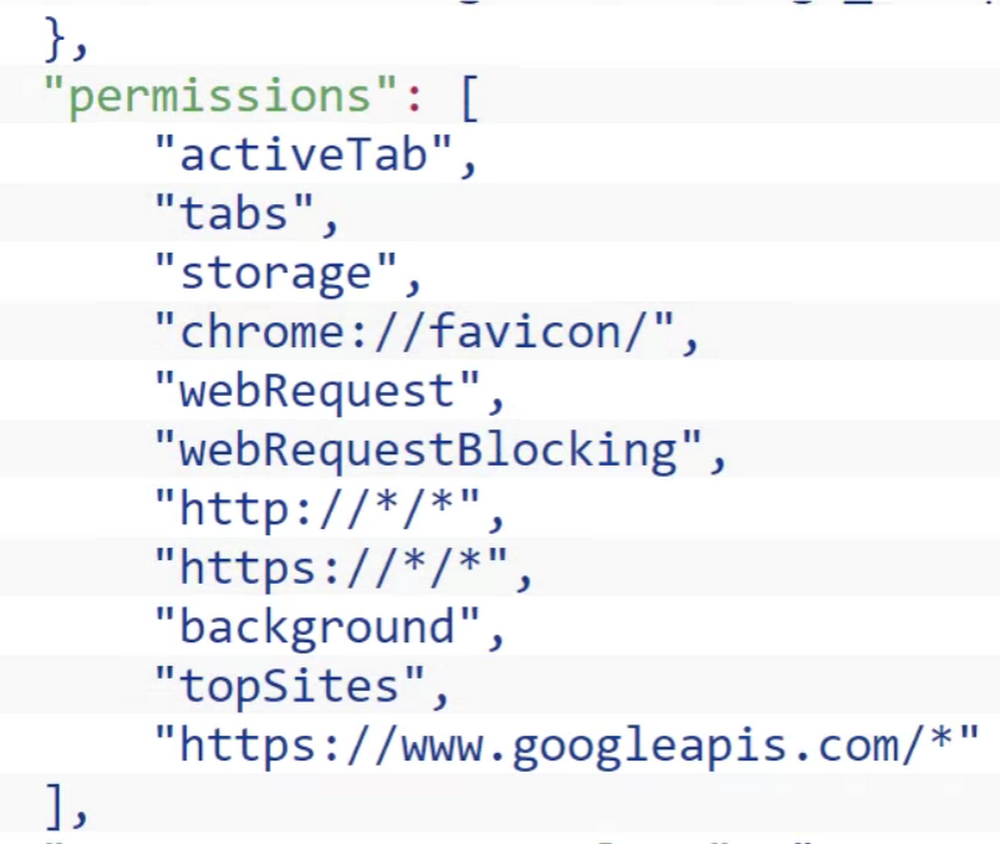
Take a look at this list of the various permissionsto help you determine what is or isn’t acceptable to be run on your organization’s devices. As a first step towards discovering which extensions are live in your environment, consider Chrome Browser Cloud Management. It has the ability to pull what extensions are present on your enrolled machines as well as what permissions they are using. Here is an example of that view in Chrome Browser Cloud Management:
If you’re a G Suite customer, you already have this functionality in the Device Management section of the Admin console.
Once you’ve done a discovery exercise to learn which extensions are installed on your end users’ machines, and created a baseline of what permissions you will (or won’t) allow in your environment, you can centrally allow or block extensions by those permissions. With this approach, you don’t have to maintain super long whitelists or blacklists. If you couple this with allowing/blocking site permissions, which allows you to designate specific sites where extensions can or cannot run, you add another layer of protection. This approach of blocking runtime hosts makes it so you can block extensions from running on your most sensitive sites while allowing them to run on any other site.
For a more in depth look at managing extensions, check out this guide (authored by yours truly) that covers all of the different ways of managing extensions. Or watch this video of me and my Google Security colleague, Nick Peterson, at Next 2019 presenting how to get this done. Enjoy, and happy browsing!




